Turn Security Testing into Continuous Assurance
Strengthen security posture with automated, continuous penetration testing.
Book a DemoIdentify real-world exploit paths across APIs and applications with continuous, agentic penetration testing.
Automated API Penetration Testing for Modern Security Teams
Security teams face expanding cloud infrastructure, microservices, and API ecosystems. Traditional pentests provide snapshots, while attackers operate continuously. Security leaders must demonstrate proactive risk management, breach resilience, and measurable security posture improvements across dynamic environments.
APIs now represent the largest web attack surface
95% of organisations report API security concerns
Point-in-Time Pentests Leave Security Gaps
Annual penetration tests and vulnerability scans create long periods without validation. Security teams lack visibility into newly deployed APIs, configuration drift, and evolving attack paths. This creates audit pressure, incident response strain, and executive scrutiny when breaches occur.
24/7 API penetration testing
Real attack-path validation
Exploitability-based risk prioritization
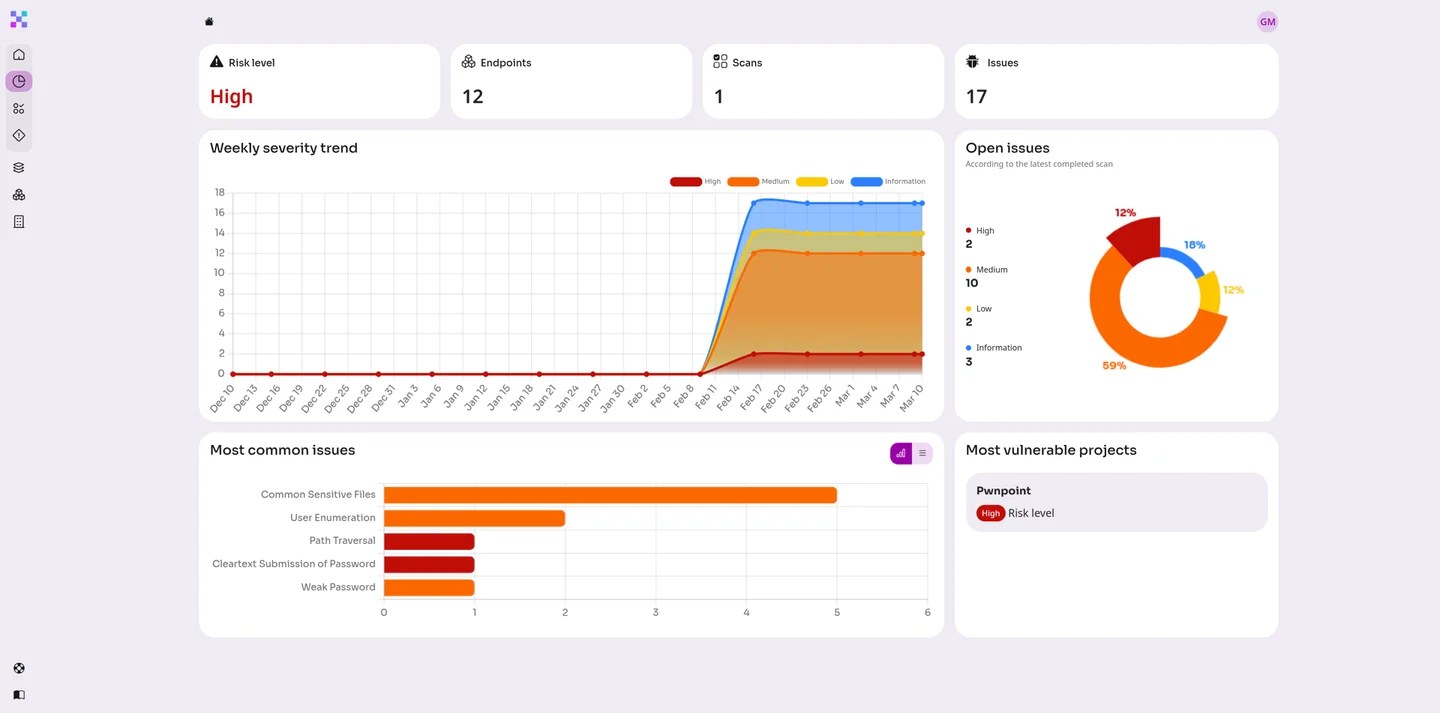
Equixly continuously maps and tests your live APIs, validating authentication flows, authorisation controls, and business logic. As environments evolve, new attack paths are automatically assessed, giving security teams persistent visibility rather than periodic snapshots.
Equixly performs real-world attack simulation aligned with modern offensive techniques, including API abuse, privilege escalation, and logic manipulation. Rather than flagging isolated findings, it validates full exploit paths that demonstrate real business impact.
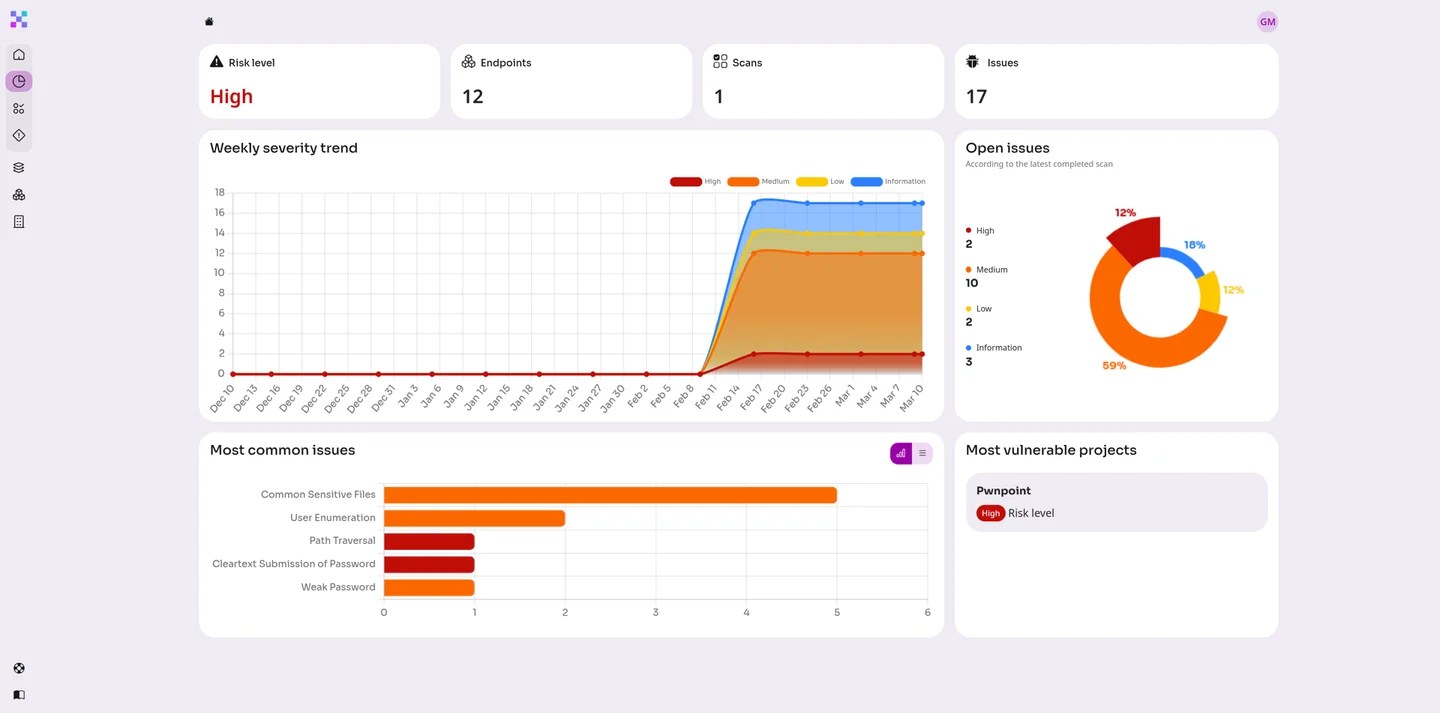
Equixly provides risk-based reporting that quantifies exploitability and remediation progress. Security leaders gain trend visibility across APIs, enabling board-level reporting and improved cyber risk governance.
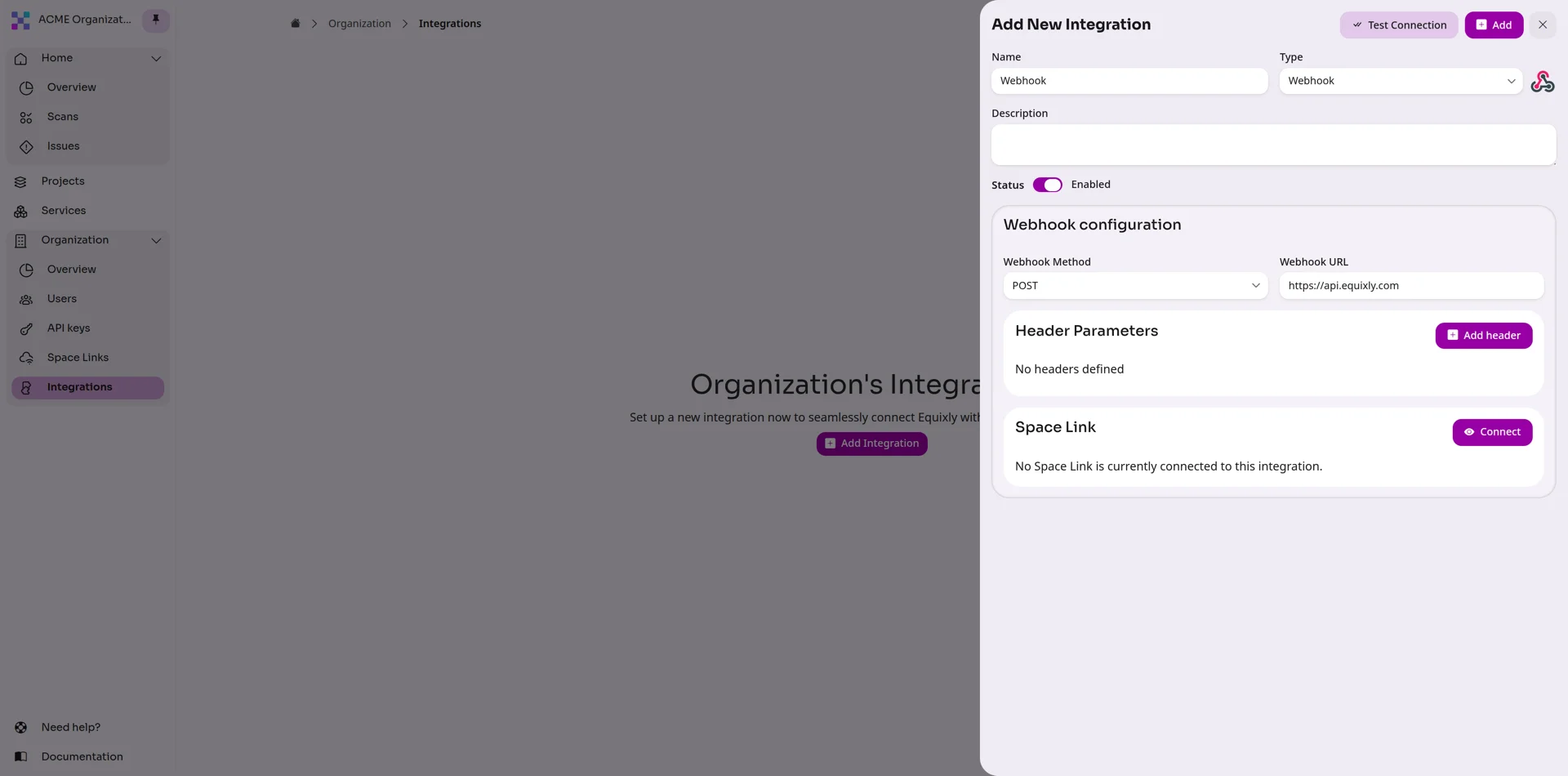
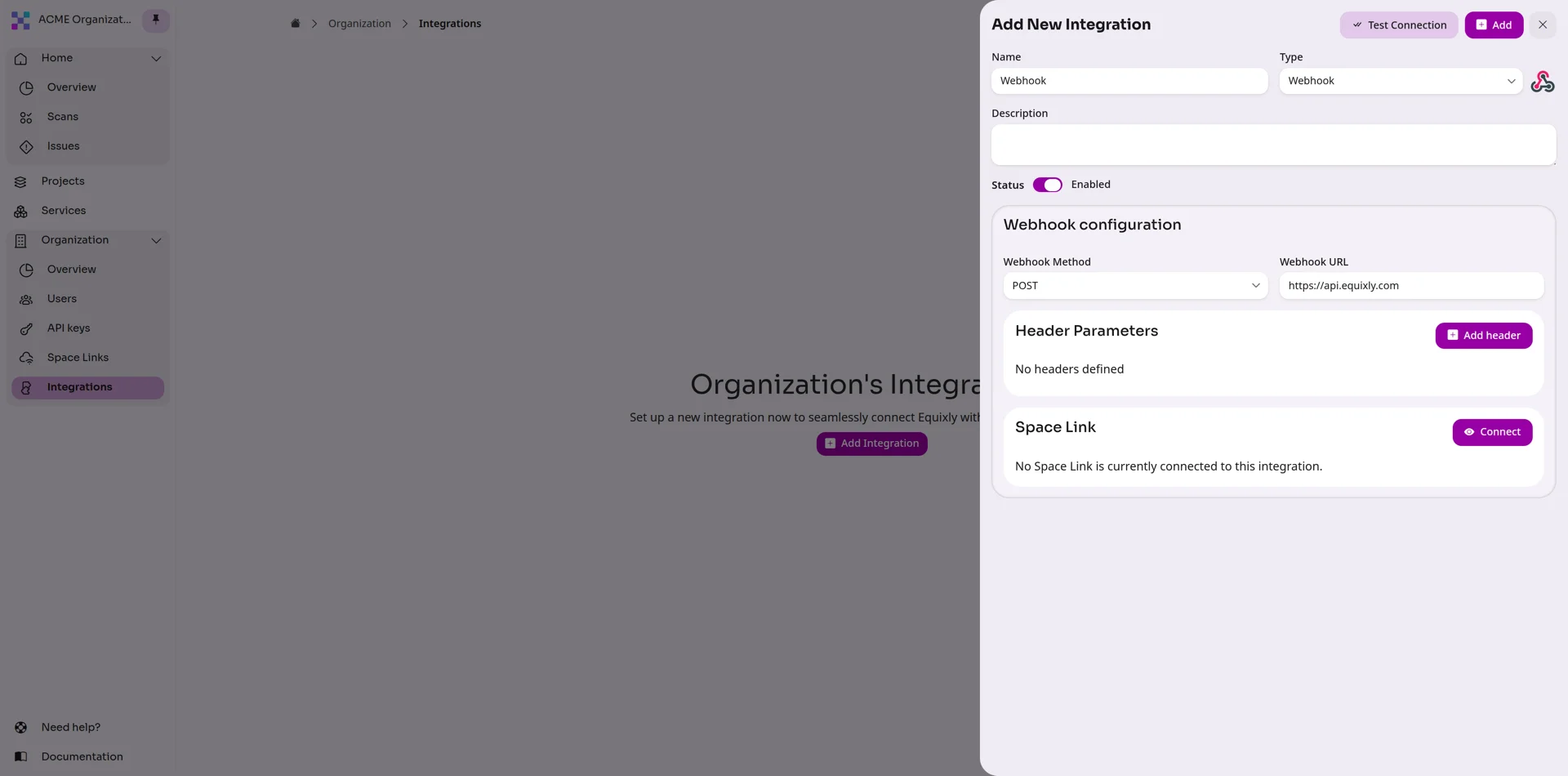
Equixly integrates alongside SAST, DAST, SIEM, and vulnerability management platforms. It complements traditional controls by validating exploitability across APIs in real-world conditions.
Traditional penetration testing is typically annual or bi-annual and manual. Equixly provides continuous API penetration testing, ensuring that new vulnerabilities, configuration changes, and deployment updates are validated regularly rather than once per year.
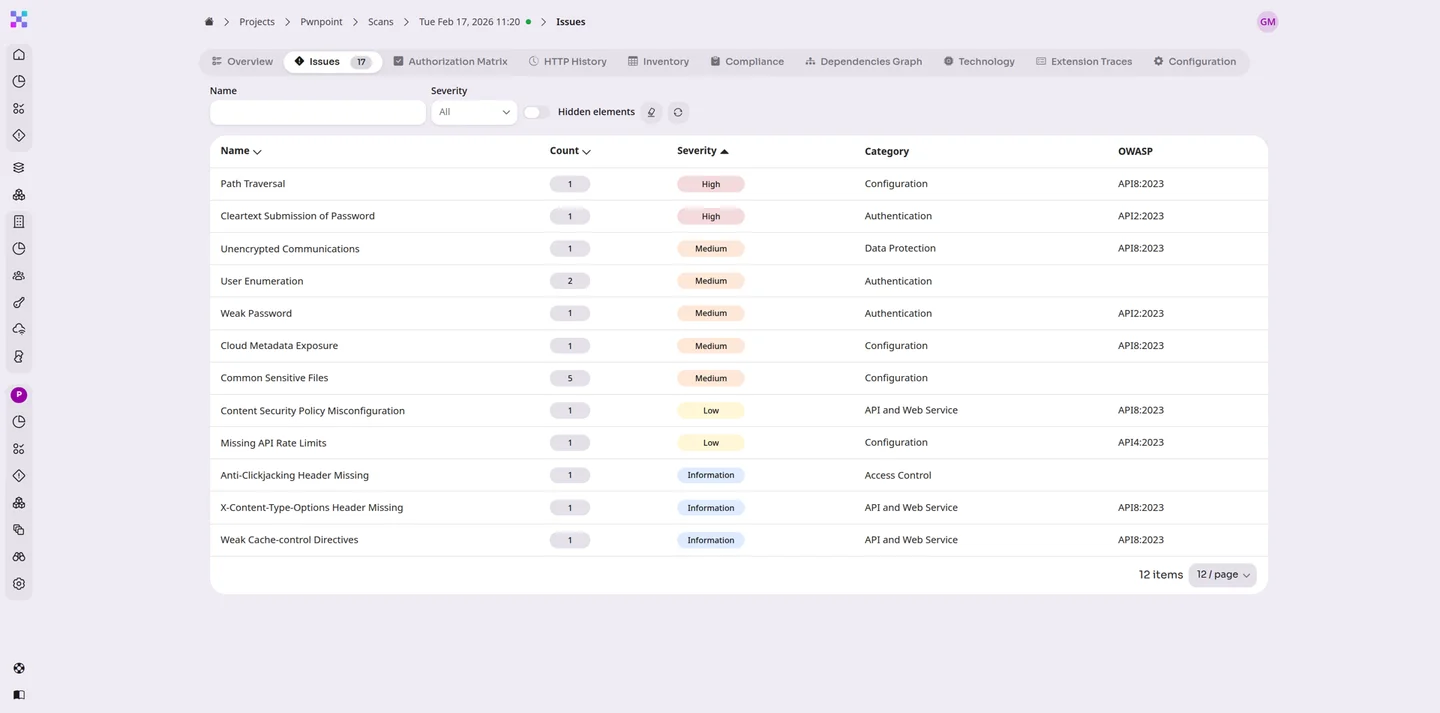
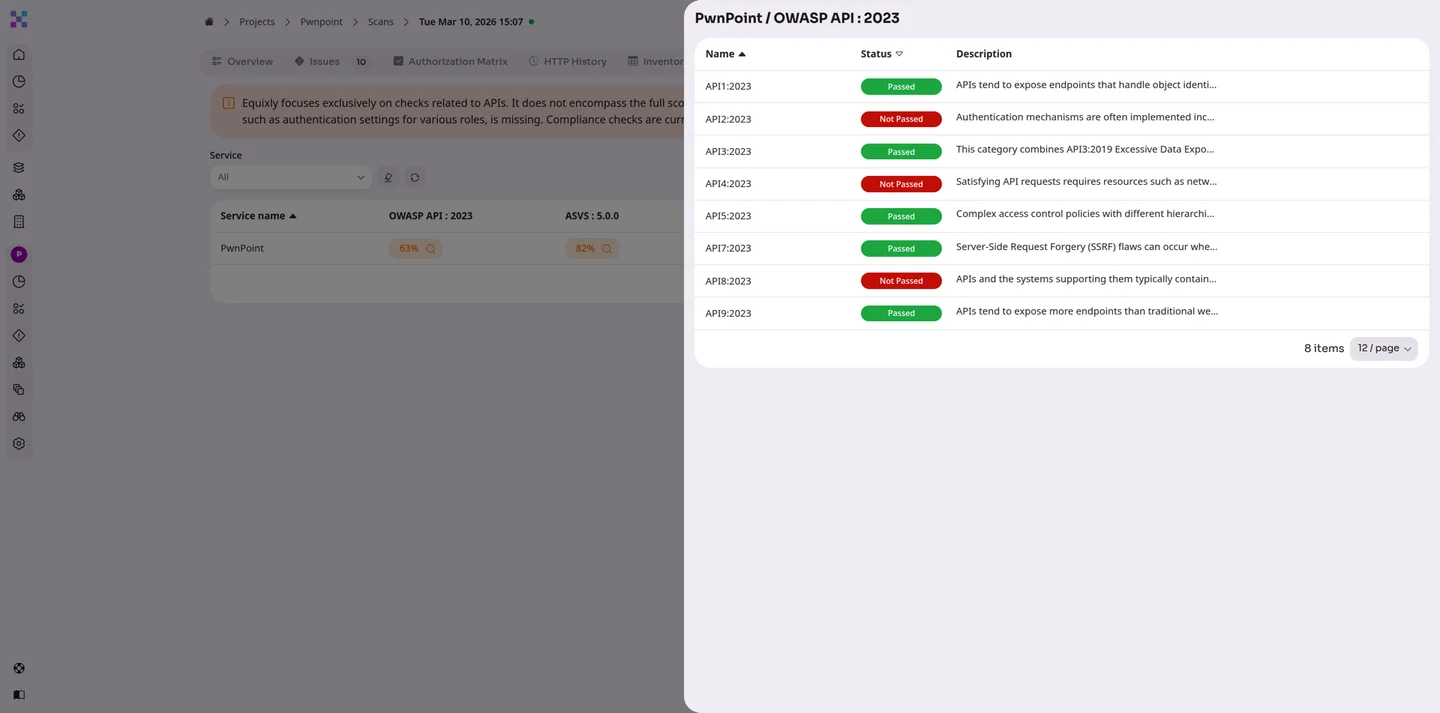
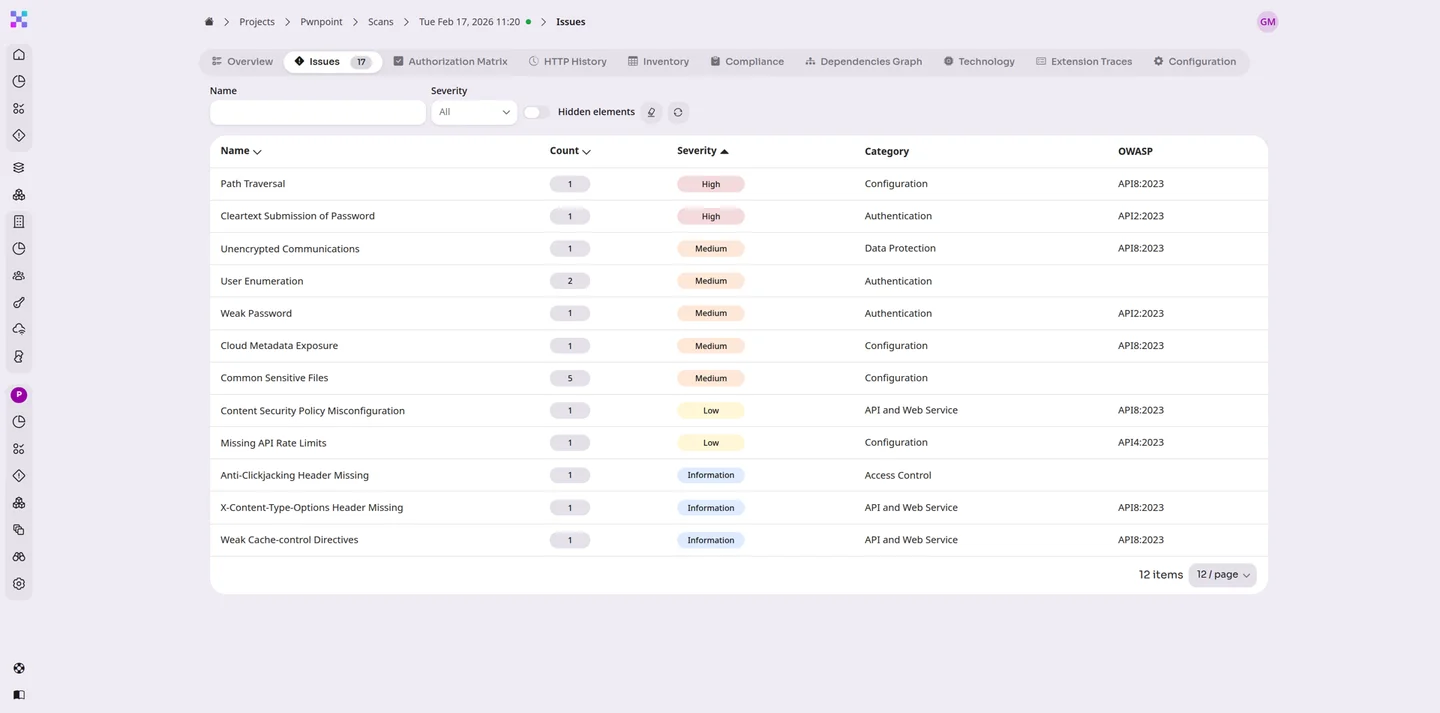
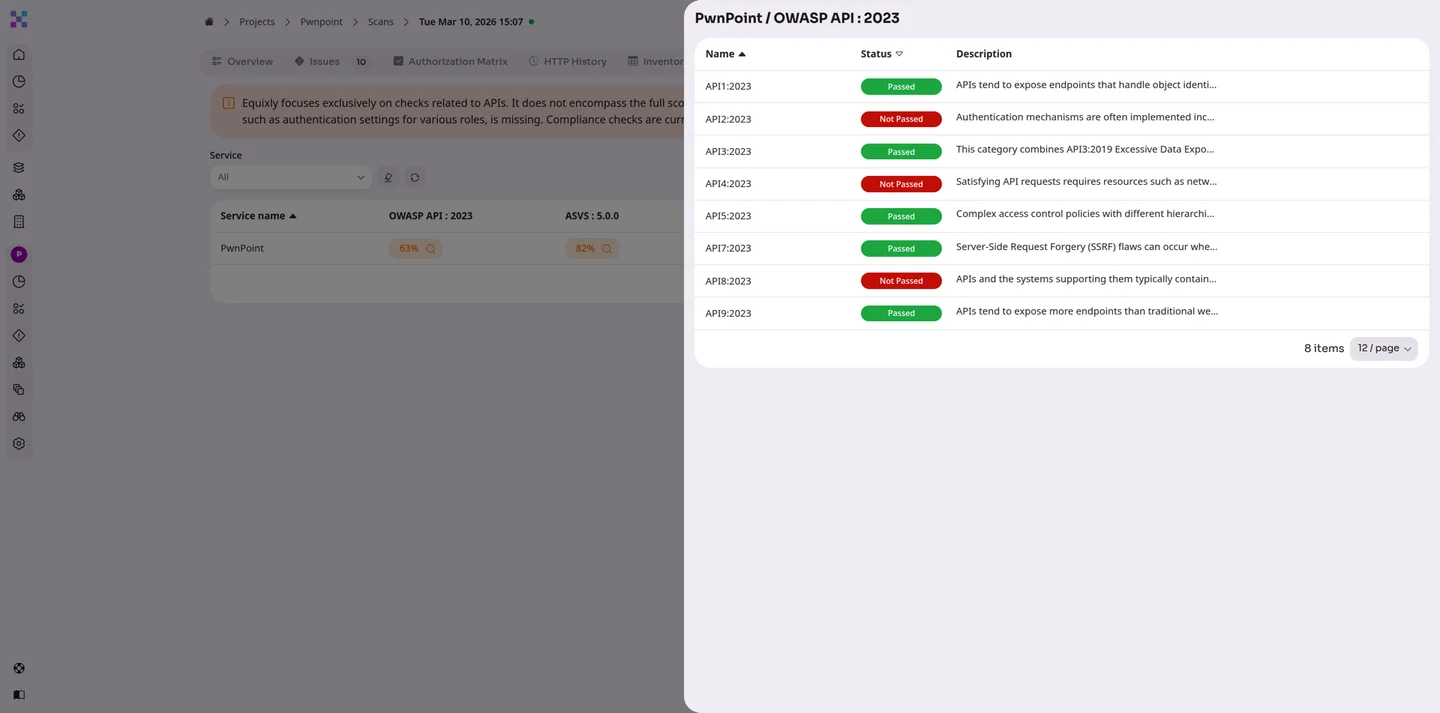
Yes. Equixly tests for vulnerabilities aligned with the OWASP API Top 10, including broken object-level authorisation (BOLA), broken authentication, excessive data exposure, and security misconfiguration -- while also validating exploit chains beyond checklist testing.
Yes. Continuous penetration testing strengthens compliance with frameworks requiring regular security validation, including DORA, NIST guidance, and ISO 27001 Annex A controls relating to vulnerability management and testing effectiveness.
Testing can run continuously or at scheduled intervals aligned with deployment cycles. This ensures validation after releases, configuration changes, or infrastructure updates.
No. Equixly focuses on exploitability-based findings. Instead of generating large volumes of theoretical vulnerabilities, it prioritises issues that can be actively exploited.
Yes. Testing is designed to be non-disruptive and controlled, ensuring real-world validation without impacting service availability or data integrity.