Continuous penetration testing and the OWASP API Security Top 10
Zoran Gorgiev, Gavin Sutton

Many organizations treat a completed penetration test as evidence of security. It isn’t. It’s evidence that a specific group of pentesters, working within a defined scope, on a fixed date, didn’t find a breach path. And that’s a much narrower statement.
The OWASP API Security Top 10 describes the vulnerabilities in production APIs — the ones attackers exploit regularly. Pentesters are absolutely adept at discovering these. But the problem is that once-a-year or even four-times-a-year tests are so disproportionately out of step with ongoing software changes, as well as threat developments, that they’re just a drop in the ocean.
What’s more, periodic penetration testing creates an utterly distorted picture of your organization’s security posture. It gives rise to a false sense of security that, in the current cyber landscape, is more of a problem than a solution.
Here, we’ll look at the OWASP API Security Top 10 risk categories through the lens of continuous penetration testing, as opposed to traditional penetration testing. To build our case for continuous penetration testing, we’ll draw on the argument Gartner developed in its recent report “The Future of Pen Testing Is Continuous Offensive Security Testing” (Poole et al., 2026).
A traditional penetration test is a snapshot. APIs are a developing organism
Unfortunately for us all, the API attack surface doesn’t become dormant between penetration tests. Your developers push new endpoints, change authorization logic, deprecate old versions, and integrate third-party services. Each of these has the potential to introduce new vulnerabilities or reintroduce old ones (those that a previous pentest flagged and fixed).
Moreover, a risk profile of an API that wasn’t exploitable yesterday changes the moment a new vulnerability is disclosed and weaponized. And threat actors have become extremely skillful at weaponizing novel CVEs.
Add to this the democratization of hacking enabled by recent developments in automation and artificial intelligence, and you begin to form a more comprehensive picture of the current challenges facing security teams.
As Gartner notes, every gap between assessments is an unvalidated exposure window, and that window is exactly where attackers operate (Poole et al., 2026). From this perspective, the idea of offensive SOC, but built around scaled continuous penetration testing (and attack surface management), is becoming a realistic necessity.
To summarize, this necessity rests on a factual observation:
- Software development is dizzyingly dynamic.
- The current attack surface is extremely volatile.
- Therefore, a static testing schedule is becoming outdated and dangerous.
Authorization flaws: Risks that live inside your business logic
Three of the top 10 risks — Broken Object Level Authorization (BOLA), Broken Object Property Level Authorization (BOPLA), and Broken Function Level Authorization (BFLA) — are authorization failures. Together, they account for the most common, most exploited API vulnerabilities.
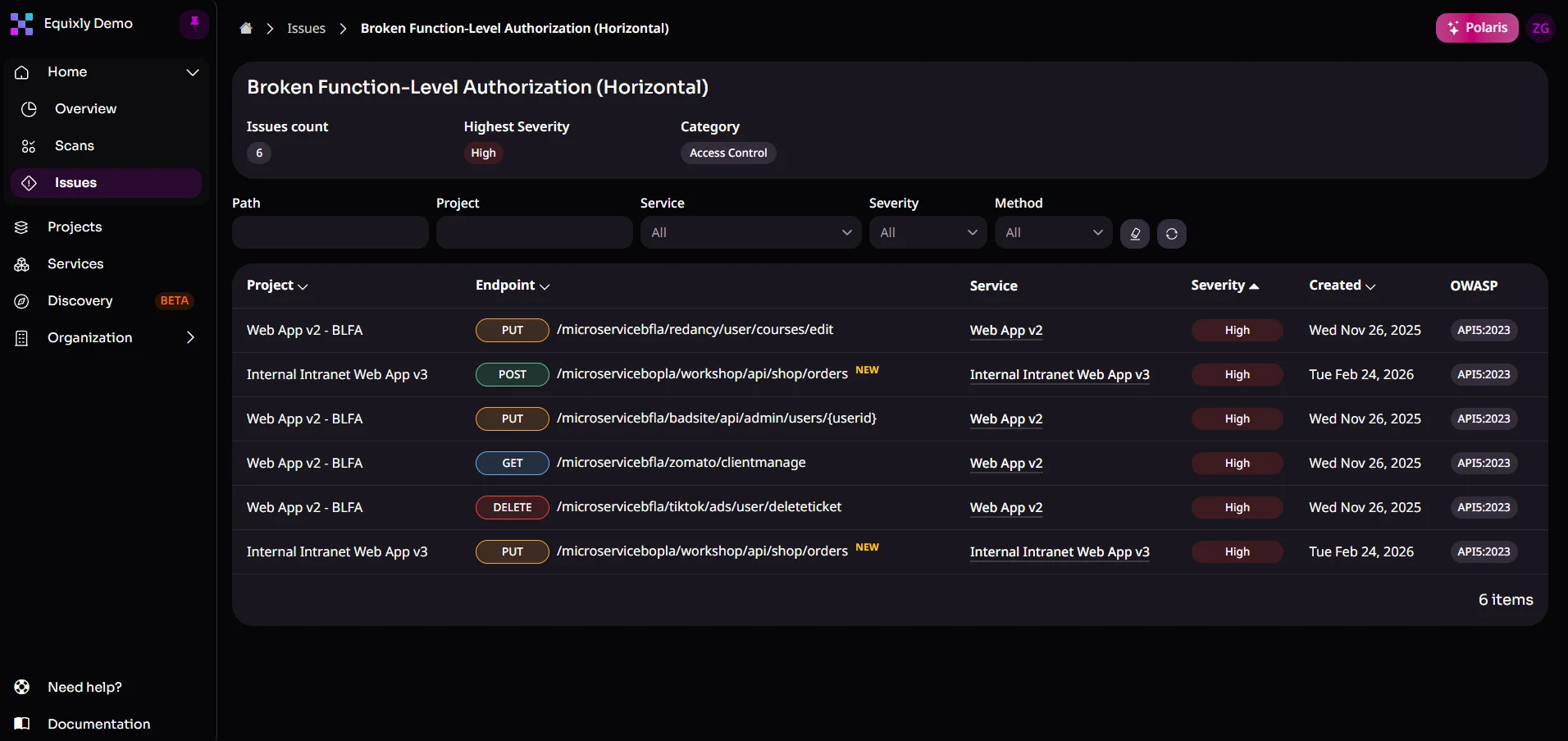
What makes these hard to discover in a single penetration test is that they are not classic technical weaknesses. They are logic failures unique to your application’s data model and permission design. It can easily happen that an API that correctly enforces authorization for today’s data types may expose a new resource after a new feature release. And it can do so without any deliberate security regression.
Continuous penetration testing is the optimal way to test for authorization flaws because it probes the same endpoints over and over after code changes. If your development team introduces a new resource type without updating the authorization matrix, a continuous testing cycle catches it in the next run, not 12 months later. And that’s about as clear a benefit as you can get.
Precisely because it changes constantly, as well as because of the prevalence and severity of authorization weaknesses in APIs, authorization logic is a primary target for Equixly’s Agentic AI Hacker and its multi-step attack sequences.
Broken Authentication: A moving target that attackers always probe
Broken Authentication (API2) is a vulnerability class in which automated, scalable attack techniques — such as credential stuffing, brute forcing, and token abuse — are standard practices.
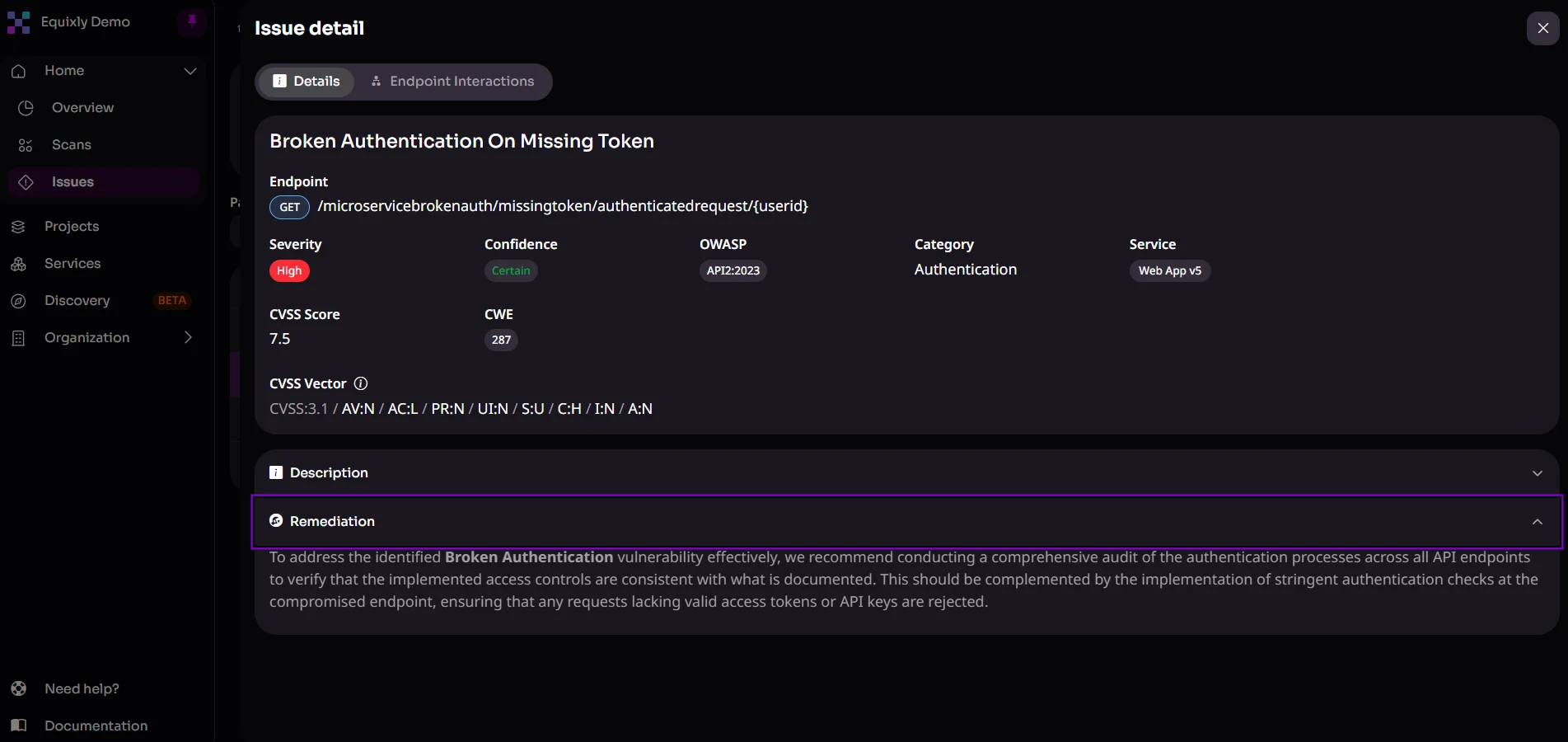
This threat never stands still. New credential databases emerge after every major breach, and attackers quickly recycle them against live authentication endpoints.
An annual security assessment gives you a yes/no answer at a single point in time: “Are your authentication controls sufficient today?” That answer becomes less reliable with every passing week.
Continuous penetration testing keeps tabs on whether authentication endpoints remain robust as the threat changes, not when the calendar says so.
Equixly tests authentication endpoints across time and changes, simulating credential stuffing, token manipulation, and brute-force attacks as part of every testing cycle. Since it runs automatically and autonomously against your live APIs, it makes it possible to catch authentication regressions the moment they appear in code.
API inventory: You can’t test what you can’t see
Undocumented endpoints, deprecated versions still connected to live data sources, and third-party-facing interfaces nobody cataloged — these unknowns exist in most production environments. And they are there precisely because API inventories are rarely maintained in real time.
Traditional pentests are scoped against what the organization already knows about its infrastructure. And zombie and shadow APIs often don’t make it into the agreed-upon scope. The reason is that the organization itself doesn’t know they exist, and a time-boxed engagement rarely leaves room for exhaustive reconnaissance and comprehensive discovery.
One way Equixly tackles this security risk is by comparing what the Agentic AI Hacker observes during testing against the API specifications. Anything the backend accepts that isn’t in the specs gets flagged. That includes shadow APIs, shadow parameters, verb tampering, undocumented HTTP methods, and older API versions still running alongside the current one. If it’s undocumented but reachable, Equixly finds it.
Another way is through a classic endpoint discovery. In this case, API specs are not necessary. Instead, a base URL is sufficient for the platform to discover uninventoried API endpoints.
SSRF and Unsafe API Consumption: Vulnerabilities that cross trust boundaries
Server-Side Request Forgery (SSRF, API7) and Unsafe Consumption of APIs (API10) include trust boundaries that extend beyond your own application. In SSRF, an attacker manipulates the server into issuing requests to unintended internal or external destinations. In API10, a third-party service your API trusts becomes the attack vector.
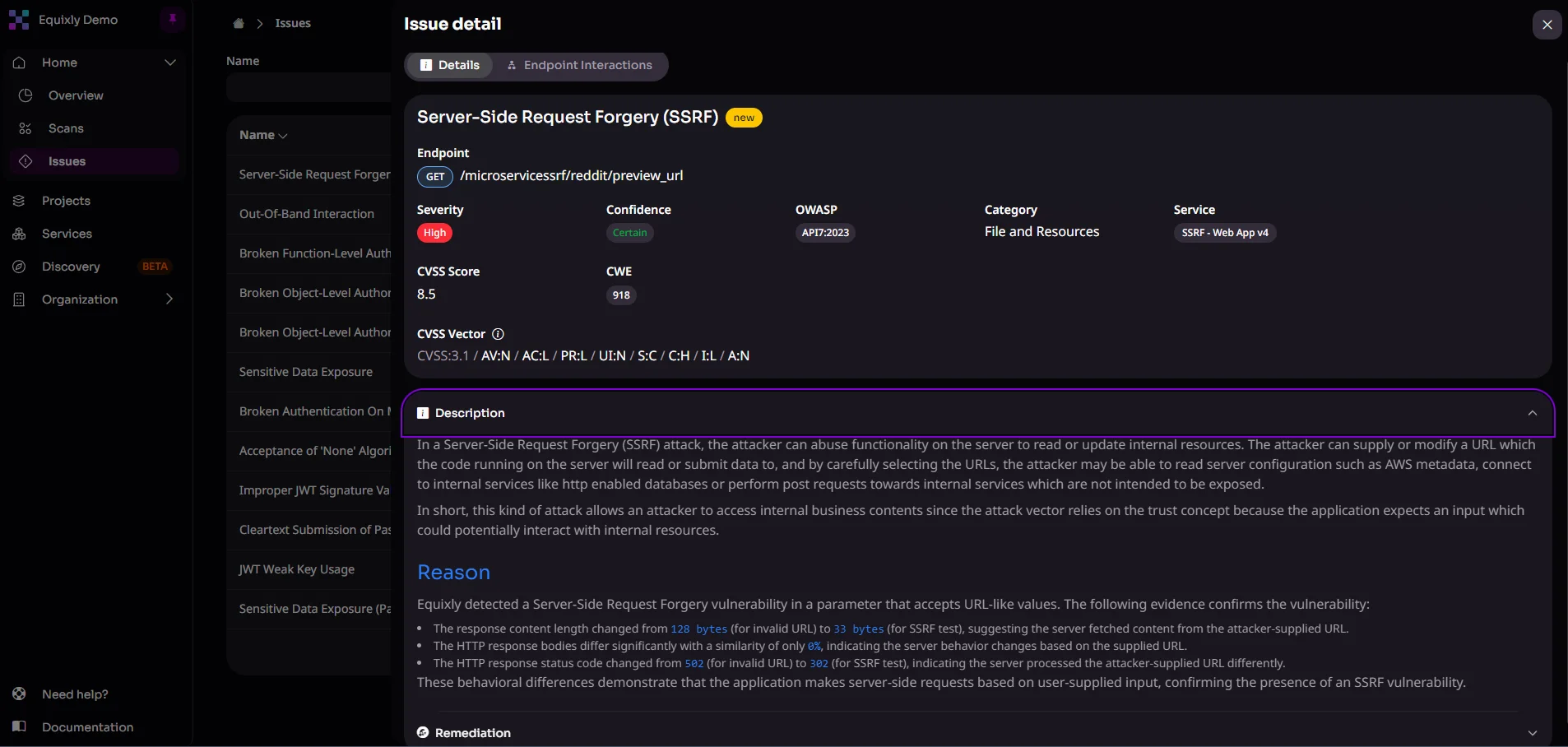
Both are notoriously difficult to catch in a one-time penetration test because they depend on the current state of your infrastructure and integrations. A microservice that didn’t exist during the last pentest may now be reachable via SSRF. A third-party API that your platform integrated last quarter may not meet your established security standards.
For SSRF and Unsafe Consumption of APIs, the Agentic AI Hacker generates intelligent payloads that attempt to trick servers into issuing unauthorized internal requests, and validates how your APIs parse and handle data from external sources.
Both types of security checks can run continuously, meaning a new third-party integration or a configuration change that opens an SSRF vector is caught in the next cycle, not at the next scheduled penetration test.
Resource abuse and business flow risks: Patterns that emerge over time
Unrestricted Resource Consumption (API4) and Unrestricted Access to Sensitive Business Flows (API6) are behavioral attacks. They require an attacker to probe for rate-limit gaps or understand business logic well enough to automate abuse.
A one-off penetration test can check whether rate limiting is configured and whether sensitive business flows have access controls in place. What it cannot do, however, is emulate the full range of attack patterns an adversary would try over days or weeks. That ranges from probing for the exact threshold at which rate limits fail to mapping business logic thoroughly enough to identify where automation tips from legitimate use into abuse.
Equixly’s platform simulates high-volume request patterns to find where rate limiting breaks down or doesn’t exist at all. In addition, it chains requests across sensitive business workflows — ticket purchases, account actions, comment flows, and similar — to find where automation can abuse the logic in ways a one-off manual test is unlikely to uncover consistently.
Both run continuously, so a rate-limiting regression introduced in a new deployment gets caught early, reducing the risk of reaching production.
Security Misconfiguration: The risk that never stops appearing
Security Misconfiguration (API8) is a repeat offender. The reason isn’t that it’s too complex; it’s simply a ubiquitous phenomenon. Misconfigured HTTP headers, exposed debug endpoints, default credentials, or overly permissive CORS policies crop up constantly. And environments with extremely fast deployment cycles are most likely to suffer from them.
Configuration divergence is one of the primary triggers that should automatically trigger a new testing cycle in a continuous offensive security model. Every deployment is a potential misconfiguration event. Waiting for the next scheduled penetration test to discover one is, in most production environments, a risk no organization with a mature security posture should accept.
Equixly triggers automated testing against each new deployment, using the Agentic AI Hacker to probe runtime behavior for unintended exposure. By validating how the API responds in practice — rather than relying on declared configurations — it surfaces misconfigurations introduced through drift, oversight, or rapid deployments.

Final thoughts
The OWASP API Security Top 10 describes threats that are always present, constantly evolving, and increasingly automated. Malicious actors don’t wait for the next security assessment. They probe continuously, adapt quickly, and capitalize on security gaps that arise between testing cycles.
Periodic penetration testing alone is no longer sufficient, especially in complex, API-first architectures. As software delivery speeds up, security validation must keep pace with change.
Gartner projects that by 2028, over 60% of enterprise pentest programs will operate as continuous validation embedded in DevSecOps pipelines, governed by continuous threat exposure management. But this prediction reflects a change that’s already underway in more mature security environments.
Equixly is built for this model. It runs alongside your development cycle, discovers vulnerabilities as they emerge, and feeds findings directly into remediation workflows, so fixes happen before attackers exploit them.
A one-off penetration test tells you where you stood. Equixly tells you where you’re standing continuously. Book a demo.
FAQs
How do we fit continuous penetration testing into a CI/CD pipeline without slowing releases?
The most important step is to scope tests to only changed endpoints and trigger them on deployment events instead of schedules, so penetration testing runs in parallel with your pipeline.
What’s the difference between vulnerability scanning and continuous penetration testing for APIs?
In general terms, vulnerability scanning matches your endpoints against known signatures and configuration checks. Continuous penetration testing, on the other hand, actively chains authorization bypasses, logic flaws, and business flow abuse attempts the way a real attacker would.
How do we avoid alert fatigue from continuous automated testing?
Risk-tier your findings so only high-severity, confirmed exploitable results trigger immediate notifications. Lower-risk items should feed only the dashboard and remediation backlogs.

Zoran Gorgiev
Technical Content Specialist
Zoran is a technical content specialist with SEO mastery and practical cybersecurity and web technologies knowledge. He has rich international experience in content and product marketing, helping both small companies and large corporations implement effective content strategies and attain their marketing objectives. He applies his philosophical background to his writing to create intellectually stimulating content. Zoran is an avid learner who believes in continuous learning and never-ending skill polishing.

Gavin Sutton
Head of Marketing
Gavin is marketing leader with more than a decade of experience in the cybersecurity industry helping startups and scale ups grow internationally. He has a passion for working with disruptive technology companies who can reshape the security landscape with their innovative solutions.